The North Korean hacker group Kumsong 121 recently launched a cyber attack using social media. Computer and mobile phone users should be wary as North Korean hacking attacks grow more sophisticated.
In a press release Tuesday, EST Security said it had detected a new “advanced persistent threat” (APT) by Kumsong 121. It said this attack employed an elaborate method: rather than email, the attackers used social media to befriend the target and send an infected file.
After hacking an individual’s social media account, the attackers chose additional targets from the victim’s social media friends.
The hackers lowered the guard of the target and earned their friendship by sending chat messages with friendly greetings and ordinary topics of interest or gossip.
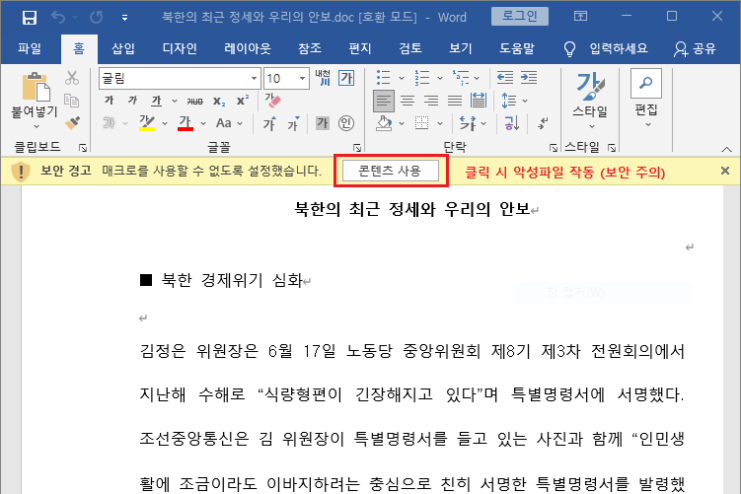
The attackers then sent an infected document file to the target through email by soliciting advice on a column related to North Korean affairs they claimed to have recently written.
The attached document file contains a macro virus that renders the target’s computer hackable if the email recipient approves the file.
The attackers essentially grafted social media onto traditional “spear phishing” attacks aimed at particular individuals.
In fact, a North Korean hacking group recently attempted to distribute an infected file by hijacking the social media account of a North Korean defector and trying to chat with his friends.
Kumsong 121 is also targeting Android smartphones.
According to EST Security, Kumsong 121 is carrying out “smishing” attacks aimed at Android smartphone users. If victims install an infected Android package created by the hackers, much of their private information gets leaked, including the address books, text messages, phone records, location information, sound recordings and photos saved on their phones.
Mun Chong Hyun, the head of the ESTsecurity Security Response Center (ESRC), said Kumsong 121 has hacked the mobile phones of well-known figures, including a certain South Korean lawmaker, stealing their private information. He said the hackers attack the websites of groups working in the North Korea space or create fake Facebook accounts to continuously target individuals working in the North Korea sector.
“In particular, they often use mobile phones or email to contact you, pretending to be an acquaintance or industry expert,” he said. “When sent .apk or .doc files, the safest thing is to directly call the sender and confirm whether they are legit.”